OctoPi Remote Access in 2026: OctoEverywhere, Tailscale, and the Pi-Side Setup That Keeps It Safe
What OctoPi actually is, and why “OctoPi remote access” is a different question from OctoPrint remote access
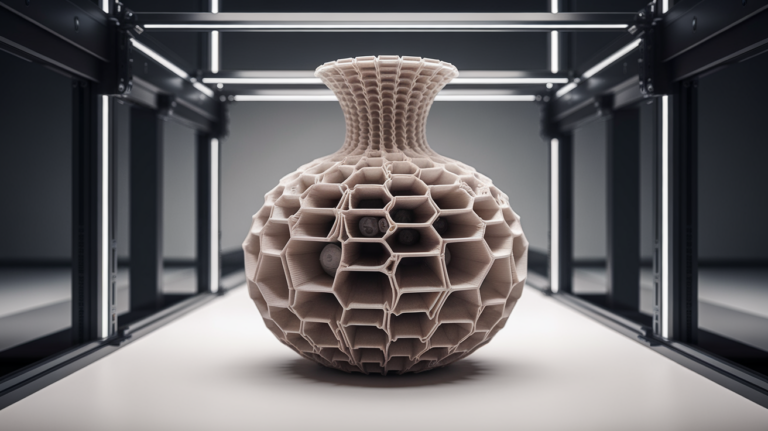
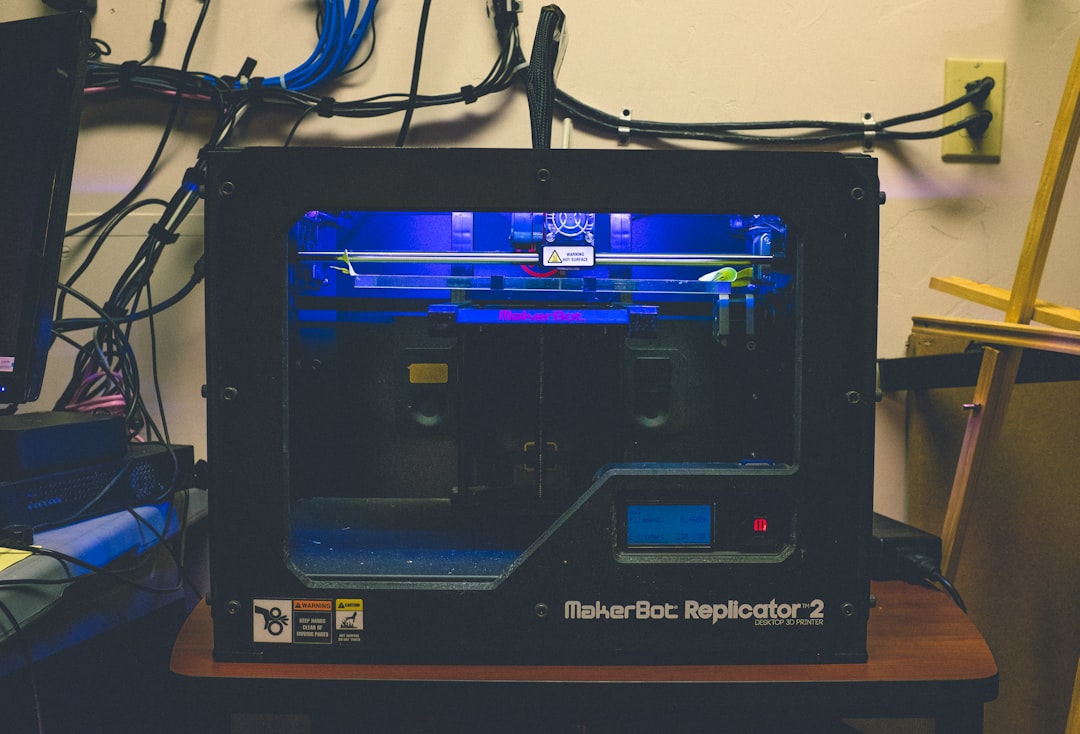
OctoPi is a Raspberry Pi OS image maintained by Guy Sheffer that ships pre-configured with OctoPrint, mjpg-streamer for camera support, and the dependencies a Raspberry Pi needs to run as a 3D printer host. When you flash an SD card with OctoPi and boot it, you get a working OctoPrint server in about three minutes without touching a single Linux command. The community usually calls it OctoPi to distinguish it from manually installing OctoPrint on Raspbian or Ubuntu.
The remote-access question for OctoPi is therefore not just about OctoPrint plugins. It is also about the Raspberry Pi underneath: SSH access, network configuration, default user accounts, security updates, and the firewall behaviour of the Pi itself. A pure OctoPrint install on a fully-managed home server has none of these concerns; an OctoPi setup running on a Raspberry Pi 4 sitting next to your printer has all of them.
This article walks through the three remote-access paths that work in 2026, then covers the Pi-side configuration that makes any of them safe. If you have read OctoPrint plugin tutorials already, the OctoEverywhere section will be familiar — but the security and Pi-side steps below are what makes the difference between a hobbyist setup that works and one that becomes a botnet entry point three months later.

The three remote-access paths and which one to pick
Path one is OctoEverywhere, a managed cloud relay that ships as an OctoPrint plugin and is included by default in modern OctoPi images. You install the plugin, link your account, and OctoEverywhere proxies traffic from your phone or browser to your Pi without needing any port-forwarding or VPN setup. Free tier covers everyday home use; paid tiers add features like webcam streaming bandwidth boosts.
Path two is direct port forwarding on your home router. You expose port 80 (HTTP) or 443 (HTTPS) on your router and point it at the Pi. This works but is the least safe option in 2026 because OctoPrint’s authentication is not designed to face the open internet, and Raspberry Pi OS itself receives security patches less aggressively than a proper server distribution. Most users should not do this.
Path three is a VPN — Tailscale, WireGuard, or self-hosted OpenVPN — that creates a private network between your phone and the Pi. This is the safest option, requires twenty minutes of setup, and is what I run on every OctoPi I deploy. Tailscale is the easiest version: install on the Pi, install on your phone, both join the same Tailscale network, and the Pi is reachable at a private IP address from anywhere your phone has internet. No router config, no exposed ports.
OctoEverywhere setup walkthrough
From the OctoPrint web interface, go to Settings, then Plugin Manager, then Get More. Search for OctoEverywhere and install if it is not already present (modern OctoPi images include it by default). Restart OctoPrint when prompted. After restart, the OctoEverywhere setup wizard appears in the navigation; it generates a one-time linking URL that you open on your phone or another device.
The phone or browser side asks you to log in or create an OctoEverywhere account. You confirm the link and the plugin generates a printer URL that looks like https://printer-name.octoeverywhere.com. Bookmark that URL on your phone. From now on, opening it from anywhere on the internet shows the OctoPrint interface for your Pi. The plugin keeps the connection alive in the background; you do not need to do anything else on the Pi.
What OctoEverywhere does under the hood is open an outbound WebSocket connection from your Pi to its cloud relay. Your phone connects to the relay, the relay forwards to your Pi over the WebSocket. Because the connection is initiated outbound from the Pi, no inbound port forwarding is needed and your home network’s NAT keeps the Pi shielded from inbound internet traffic. The traffic itself is encrypted end-to-end with TLS.
Why direct port forwarding is the wrong default in 2026
Exposing OctoPrint directly to the internet means anyone scanning IPv4 address ranges (which is constant background activity) finds your printer within a week. OctoPrint requires authentication, but its auth system is not designed to resist a brute-force attack from a botnet trying ten million password combinations. There have been documented cases of OctoPrint instances getting taken over and used as ransomware launchpads.
If you must port-forward — for example because your ISP CGNAT prevents OctoEverywhere from working reliably and Tailscale is somehow blocked — at least put OctoPrint behind a reverse proxy with HTTPS, change the default username, set a strong unique password, enable the OctoPrint access control plugin, and enable HAProxy or nginx with rate limiting. Even with all of that, you are running an internet-exposed unmaintained-grade web service. Do not do this on a Pi that also runs anything else important on your network.
The threat model people usually overlook is that compromise of the Pi gives the attacker LAN access. From there they can scan your other home devices, network-attached storage, IP cameras, and router admin interface. A compromised OctoPi is rarely the goal; it is a stepping stone to whatever else is on your home network. Keep this in mind when weighing convenience against security.
Tailscale VPN: the practical safe option
Install Tailscale on the Pi with curl -fsSL https://tailscale.com/install.sh | sh, then run sudo tailscale up. The command prints a URL that you open in a browser to authenticate. Once authenticated, the Pi joins your Tailscale network and gets a stable 100.x.x.x address. Note that address. Install Tailscale on your phone and authenticate with the same account; both devices now share a private network.
From your phone, open a browser to http://100.x.x.x (the Pi’s Tailscale address) and the OctoPrint interface loads exactly as if you were on the home Wi-Fi. The connection is end-to-end encrypted with WireGuard, the Pi is not exposed to the open internet, and your home router does not need any reconfiguration. Battery impact on the phone is negligible — Tailscale uses about 2-5% extra battery in continuous operation, less if you only enable it when needed.
For users who travel internationally or hop between hotel Wi-Fi networks, Tailscale is more reliable than OctoEverywhere because it does not depend on the cloud relay’s regional availability. The downside is that you carry the responsibility of keeping the Pi’s Linux side patched and the Tailscale daemon updated. A monthly sudo apt update and sudo tailscale update keeps things current.

Pi-side hardening that applies regardless of remote-access method
Change the default user. Old OctoPi images shipped with a pi user and password raspberry; modern images force you to set a new username on first boot. If you are running a long-lived OctoPi from before that change, create a new user, give it sudo access, and disable the pi user with sudo passwd -l pi. This single step blocks the most common automated attack on Raspberry Pi servers.
Set a strong password and disable password-only SSH if you can. Use SSH keys: generate a key pair on your laptop with ssh-keygen, copy the public key to the Pi with ssh-copy-id, then edit /etc/ssh/sshd_config to set PasswordAuthentication no. Test that you can still log in with the key before closing the existing SSH session, otherwise you may lock yourself out and need to flash a new image.
Enable automatic security updates with sudo apt install unattended-upgrades and sudo dpkg-reconfigure -plow unattended-upgrades. The Pi will then install security patches without asking. Reboot weekly to apply kernel updates that require restart; sudo apt install cron-apt or a simple cron job at 3 AM Sunday handles this.
When remote access becomes more trouble than it is worth
If your only use case is “start a print before bed and check the timelapse in the morning”, you might not need remote access at all. A camera pointed at the printer with a separate locally-stored timelapse, plus the printer’s onboard touchscreen, covers that workflow with no internet exposure. Adding remote access doubles the attack surface for one convenience feature.
The strongest reason to add remote access is monitoring while away from home — visualising progress, intervening on a failed print, getting a notification when something is wrong. For that workflow OctoEverywhere or Tailscale are both excellent. The weakest reason to add remote access is “I might need it someday”; if you do not have a concrete use case, leave the Pi on the home network and avoid the security overhead.
Final picks by user type
For the casual home user who wants the easy path and is comfortable with cloud services, install OctoEverywhere from the OctoPrint plugin manager and stop reading. The free tier covers everyday use, the configuration takes five minutes, and the security posture is reasonable thanks to the outbound-only WebSocket model. This is the recommendation for at least 80% of users searching for OctoPi remote access.
For users who already use Tailscale or another mesh VPN for general remote access (NAS, home Assistant, security cameras), add the Pi to the same network and skip OctoEverywhere entirely. One VPN to manage is fewer surfaces for a security mistake. Tailscale is genuinely the cleaner long-term answer for technically capable users; it is the recommendation for the next 15% of the audience.
For everyone else — users with weird ISP CGNAT setups, users in countries where Tailscale or OctoEverywhere are blocked, users with very specific corporate-style security requirements — the answer is bespoke and beyond the scope of a single article. Consider self-hosted WireGuard on a VPS, or a reverse-proxy-and-Cloudflare-Tunnel setup. The principle is the same: do not expose OctoPrint directly to the internet, do keep the Pi patched, and do periodically audit who has access. With those rules in mind, every remote-access path becomes safe enough to use confidently.